Key Takeaways
- Social engineering scams caused billions in crypto losses in 2025–2026, with most attacks targeting human behavior instead of smart contract vulnerabilities.
- Public blockchain transparency allows scammers to identify high-value wallets, analyze activity, and launch highly targeted phishing or impersonation attacks.
- Privacy tools like RocketX Private Swaps and Monero Rails help reduce wallet visibility, making it harder for scammers to identify and profile you.
- Strong security requires multiple layers: hardware wallets, transaction privacy, fresh wallets, approval management, and strict verification habits.
- In crypto, protecting your assets is not only about securing keys—it’s also about controlling how much information attackers can see about you on-chain.
Introduction
Social engineering scams manipulate victims into revealing private keys or approving malicious transactions not just by breaking code but also by exploiting human psychology. In 2025, cryptocurrency fraud stole $11.36 billion, with investment scams ($7.2 billion) and impersonation attacks (up 1,400%) leading the threat landscape.
According to the FBI’s 2025 Internet Crime Report, crypto fraud losses rose 22% from 2024. More critically, AMLBot found that 65% of investigated theft cases involved social engineering rather than technical smart contract exploits.
Hackers don’t need to break your encryption when they can simply ask for your keys.
The math is brutal: billions lost not to code vulnerabilities, but to human decision-making under pressure, urgency, and emotional manipulation. Technical security—hardware wallets, multi-signature setups, and smart contract audits—has largely been solved. But social engineering exploits what cannot be patched: you.
This guide breaks down the 2025-2026 scam landscape and provides actionable defenses, including how transaction privacy tools like RocketX Private Swaps eliminate your visibility to scammers before they even identify you as a target. If they can’t see your holdings, they can’t target you.
What Are Crypto Social Engineering Scams?
Crypto social engineering scams are attacks where scammers manipulate victims into voluntarily compromising their own security through psychological tactics rather than technical exploits. Common methods include phishing (fake websites that steal credentials), impersonation (posing as customer support or influencers), romance scams (“pig butchering” that builds relationships before introducing fake investments), and investment fraud (Ponzi schemes and fake trading platforms). These attacks exploit trust, fear, urgency, and greed rather than breaking through cryptographic security.
Unlike hacking, which breaks through security barriers, social engineering convinces you to open the door yourself.
Why crypto is especially vulnerable:
- Irreversible transactions — Funds sent are gone forever.
- Self-custody — You are your own bank with no easy reversals.
- Blockchain transparency — Scammers use explorers (Etherscan, DeBank) and analytics tools to spot high-balance wallets and tailor attacks.
The transparency problem:
Blockchain transparency, once celebrated as revolutionary, has now become a privacy liability. Every transaction you make is permanently public. This creates the perfect hunting ground for scammers who use blockchain analysis tools to identify wallets holding large balances, track recent activity, and build comprehensive profiles of high-value targets. A whale holding $2 million in visible on-chain assets receives exponentially more sophisticated attack attempts than someone holding $5,000.
Most Common Scams in 2025–2026
| Scam Type | Key 2025 Stats / Trend | Notes |
| Investment Fraud (incl. pig butchering) | ~$7.2 billion (FBI) | Largest category; often uses fake platforms showing fabricated profits |
| Impersonation Scams | 1,400%+ YoY growth (Chainalysis) | Fake support via Discord, Telegram, X, and email |
| Phishing | Major driver of $306M in Q1 2026 Web3 losses (Hacken) | Fake sites, malicious approvals |
| AI-Enabled Scams | 22,364 complaints, ~$893M losses (FBI) | Deepfakes, AI chatbots, voice cloning |
| Romance / Pig Butchering | High per-victim losses; part of investment fraud | Months-long grooming |
AI-driven crypto scams are accelerating fast, now generating 9x more transactions than traditional fraud. Investment scams remain the biggest threat, causing $7.2 billion in losses, often blending fake platforms, romance tactics, and Ponzi schemes. A notable 2025 case linked to Coinbase saw impersonators steal nearly $16 million, highlighting how sophisticated these operations have become.
Impersonation scams have surged by 1,400%, fueled by AI automation, data leaks, and insider access, according to Chainalysis. Meanwhile, the FBI Internet Crime Complaint Center reported 22,000+ AI-related complaints and $893 million in losses in 2025.
Overall, crypto scams reached $11.36 billion, with 65% driven by social engineering (AMLBot). A single $282 million phishing attack in Q1 2026 proved that even hardware wallet users are vulnerable to social engineering.
How Transaction Privacy Helps You
Transaction privacy acts as a protective layer by concealing your wallet balance and activity from public blockchain tracking. When your holdings aren’t visible, scammers can’t single you out for high-value, targeted attacks, making you a far less attractive target.
How Scammers Identify Victims
- Blockchain scanning → Detect wallets with large visible balances (often $500K+)
- Behavior tracking → Analyze trading habits and DeFi interactions
- Identity linking → Connect wallet activity to social profiles
- Targeted execution → Launch personalized scams based on insights
Targeted scams succeed 15–25% of the time, while generic attempts only achieve 3–5% success.
Bottom line: the more visible you are, the higher your risk.
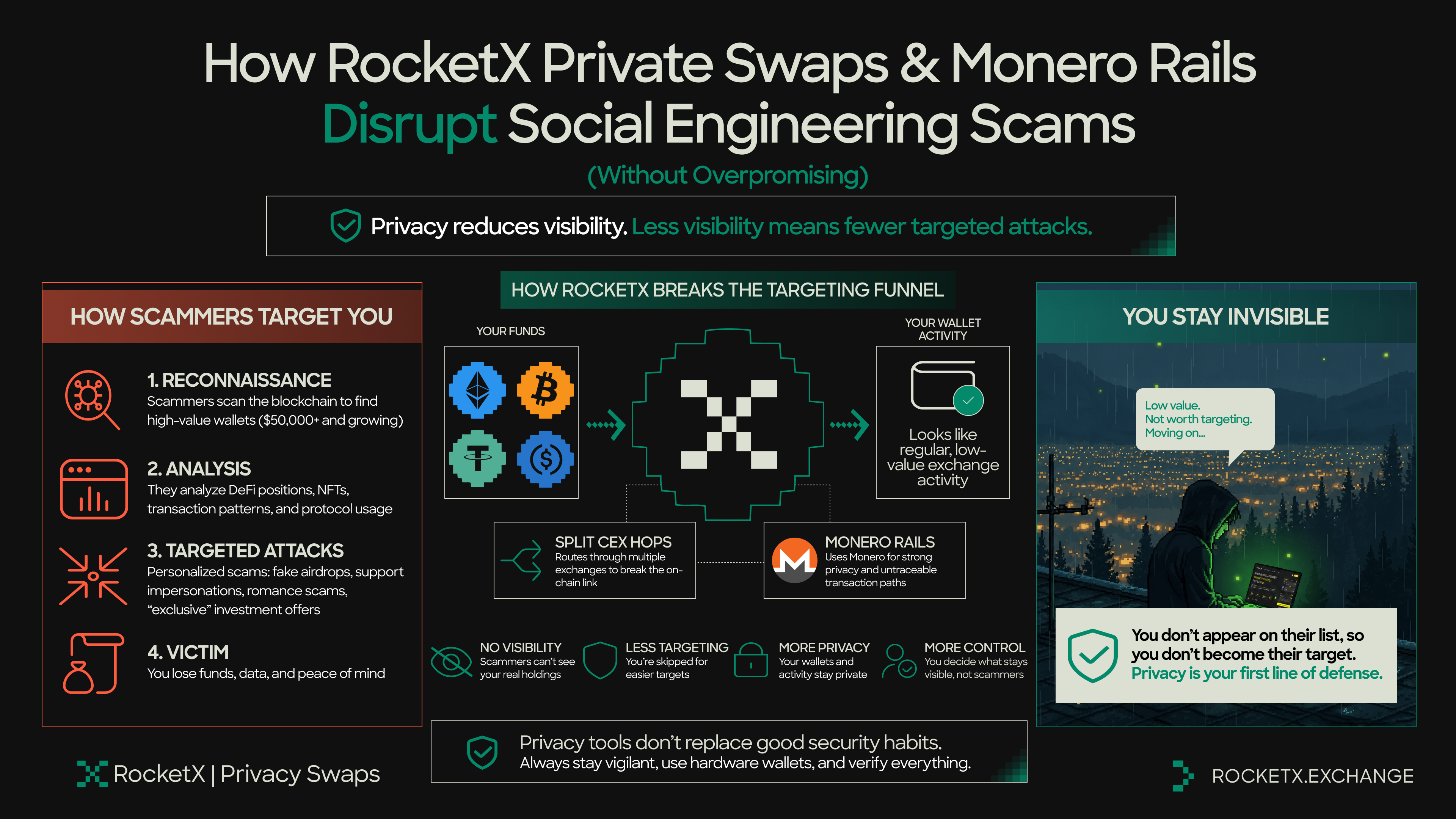
How RocketX Private Swaps & Monero Rails Disrupt Social Engineering Scams
RocketX Private Swaps and Monero Rails do not magically block phishing emails or stop a romance scammer from messaging you. What they actually do is more practical: they make you invisible during the reconnaissance phase that precedes nearly every targeted attack.
Scammers rely on blockchain scanners to identify wallets holding $50,000 or more. They analyze your DeFi positions, your NFT collection, and your transaction patterns. Then they craft personalized attacks like fake airdrop campaigns for protocols you actually use, support impersonations referencing your recent swaps, or “exclusive” investment offers tailored to your holdings.
RocketX breaks this targeting funnel at the first step. When you route funds through split CEX hops or Monero Rails, your main wallet shows only small, exchange-like activity. Your actual holdings and destination wallets remain hidden.
The scammer scanning the blockchain sees a low-value, uninteresting wallet and moves on to an easier target. This protection is indirect but powerful: you cannot be socially engineered if you never appear on the target list to begin with. It does not replace vigilance, hardware wallets, or verification habits. But for users with significant holdings, it removes the visibility that makes you a priority target.
Practical Privacy Implementation by Portfolio Size
If your holdings are $1,000 to $10,000: Use RocketX Privacy Routes for swaps above $2,000. Always swap to fresh receiving addresses.
If your holdings are $10,000 to $100,000: Use RocketX Monero Rails for all swaps over $5,000 and maintain 2–3 separate wallets and never link them on-chain.
If your holdings are above $100,000+: Use RocketX Monero Rails exclusively for significant transactions. Keep 90% + of funds in a hardware wallet and generate a fresh address for every single transaction.
Read more about How to Execute a Private Swap in 7 steps.
https://www.rocketx.exchange/blog/private-swaps-guide/
The 5-Layer Defense Framework
- Never trust unsolicited contact. Bookmark official sites, type URLs manually, and always verify through official channels only.
- Use non-custodial wallets exclusively. For holdings over $10,000, store 80–90% of funds in a hardware wallet.
- Use RocketX Private Swaps to hide your holdings from blockchain analysis. Scammers cannot target what they cannot see.
- Never share seed phrases, private keys, or passwords. No legitimate entity will ever ask for these, and 100% of such requests are scams.
- Scammers manufacture urgency to bypass rational thinking. When you feel rushed, stop completely, wait 30 minutes, and then verify independently.
What to Do If You’ve Been Scammed (First 30 Minutes)
- Secure remaining funds immediately: Create a brand new wallet with a fresh seed phrase and transfer all remaining funds right now. Assume your old wallet is fully compromised.
- Revoke all token approvals: Use Revoke.cash to remove any suspicious smart contract permissions.
- Document everything: Save screenshots of all communications, transaction hashes, and the scammer’s wallet addresses.
- Report to authorities: File a report or contact your local police, and report the scammer’s profile on the platform where the contact occurred.
Critical Warning: Never trust or pay any so-called “crypto recovery service.” According to the FBI Internet Crime Complaint Center, the vast majority of these services are secondary scams designed to exploit victims a second time.
In reality, blockchain transactions are irreversible by design, and no individual, company, or platform can undo a confirmed transfer. Claims of guaranteed recovery are a major red flag.
👉 Start using RocketX Private Swaps: https://app.rocketx.exchange
📚 Read the full privacy guide: https://www.rocketx.exchange/blog/private-swaps-guide/
Sources for Verification & Further Reading
- FBI Internet Crime Complaint Center – 2025 Annual Report
- Chainalysis – 2026 Crypto Crime Report
- AMLBot – 2025 Case Analysis
- Hacken – Q1 2026 Security Report
- Reuters – Coinbase data breach coverage (2025)
This article is for educational purposes only and does not constitute financial, legal, or security advice. Transaction privacy tools should be used in compliance with your local laws and regulations.
Frequently Asked Questions
1: Can someone steal my crypto just by knowing my wallet address?
No. A wallet address alone cannot be used to directly steal your funds. However, public wallet visibility can make you a target. Scammers use blockchain explorers and analytics tools to identify high-value wallets, monitor activity, and launch personalized phishing, impersonation, or fake investment scams. Using privacy tools to reduce wallet visibility can help lower this risk.
2: What’s the biggest cause of crypto losses from social engineering?
Investment fraud remains the largest category. According to the FBI, crypto investment scams caused roughly $7.2 billion in losses in 2025. Many begin as long-term trust-building scams, often called “pig butchering,” where victims are gradually convinced to deposit funds into fake trading platforms showing fabricated profits.
3: Can a hardware wallet prevent social engineering attacks?
Not completely. Hardware wallets secure private keys offline, but they cannot stop users from approving malicious transactions or revealing recovery phrases under pressure. Even experienced users with hardware wallets have lost funds through phishing and impersonation attacks. Hardware security reduces technical risk, but human verification remains critical.
4: How do scammers identify high-value crypto users?
Scammers commonly use blockchain analytics tools such as Etherscan, Nansen, and Arkham Intelligence to track wallets with significant holdings. They study transaction history, DeFi activity, NFTs, and behavioral patterns to craft targeted scams. Privacy-focused tools like RocketX and Monero Rails help reduce this public visibility.
5: What should I do immediately after getting scammed?
Move remaining funds to a brand-new wallet immediately, revoke suspicious token approvals, document all wallet addresses and communications, and report the incident to the relevant platform and authorities. Avoid “crypto recovery services,” as many are secondary scams targeting victims again.